Trusted by over 6,000 developers in
Build secure software for
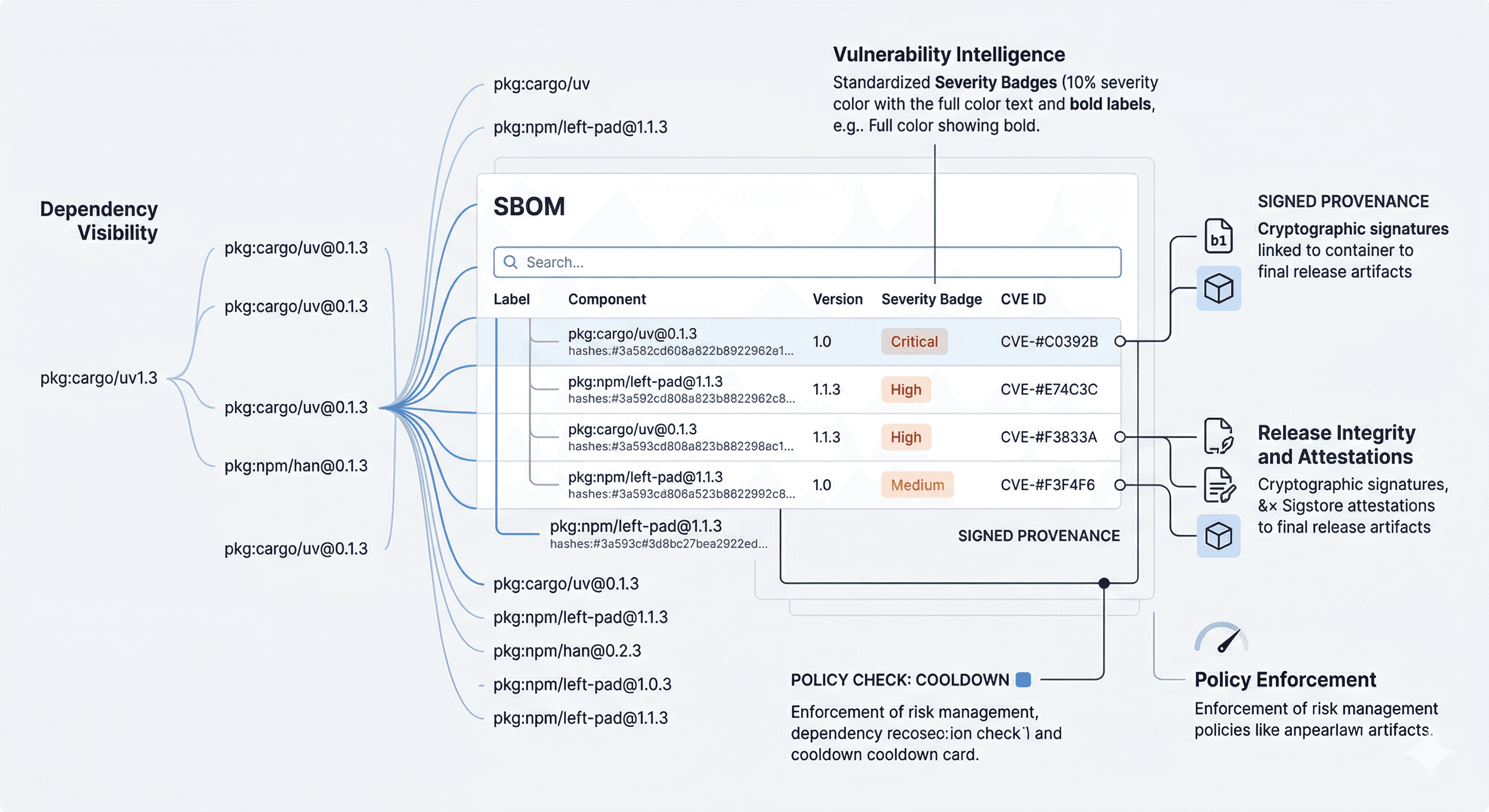
Interlynk’s AI-native SBOM platform automates secure software development to comply with global regulations.


Platform Capabilities
Contact Us for detailed information
Automated SBOM Management
Automate the creation and management of Software Bills of Materials (SBOMs) to ensure transparency, compliance, and faster response to vulnerabilities.
Continuously track and assess third-party suppliers for security, compliance, and risk posture to strengthen your overall supply chain resilience.
FDA Pain Points &
How Interlynk Helps
We simplify compliance with automated SBOMs, continuous monitoring, and ready-to-use reports
FDA Cybersecurity Requirements
Our platform automates SBOM generation, tracks open-source dependencies, and keeps your documentation FDA-ready.
Vulnerability Monitoring Across the Supply Chain
With supplier monitoring and real-time alerts, Interlynk helps you stay ahead of vulnerabilities, ensuring proactive compliance.
Demonstrating Secure-by-Design Practices
We help teams build security into their lifecycle, providing the visibility and traceability needed to demonstrate compliance confidently.
SBOM Mandates and Documentation Gaps
Our platform automates SBOM generation, tracks open-source dependencies, and keeps your documentation FDA-ready.
Managing Patch & Update Expectations
We provide continuous visibility into component vulnerabilities, making it easier to prioritize and document patching workflows aligned with FDA expectations.
Audit & Submission Readiness
We centralize your SBOMs, monitoring logs, and supplier data in one platform, making it simple to generate FDA-ready reports and streamline your compliance submissions.
What is Interlynk and what does it do?
Interlynk is an SBOM (Software Bill of Materials) automation platform designed to streamline software supply chain security, compliance, and risk management. It supports the full SBOM lifecycle—from collection and assembly through enrichment, vulnerability context, compliance validation, and secure sharing.